SECURITY, PRIVACY, & COMPLIANCE
Protect your conversations at every step

Our compliance certifications & memberships
Enterprise-level encryption
Role-based access
Single sign-on
Industry compliance across the board
Dialpad is SOC2® Type II compliant. We’ve performed a third-party audit to certify that we’ve implemented controls that operate effectively to meet the objectives of the AICPA Trust Services Principles.
Dialpad products are HIPAA-ready. Healthcare industry customers can sign a Business Associate Agreement (BAA) with one click to get up and running. For additional details, check out Dialpad's HIPAA Compliance Datasheet.
Dialpad helps organizations to meet their GDPR compliance requirements through features such as retention policies, data subject access requests, and individual consent mechanisms. Dialpad customers can sign a Data Processing Agreement (DPA) that addresses GDPR and beyond.
Dialpad is a member of the Cloud Security Alliance (CSA) Security, Trust, and Assurance Registry (STAR). You can see our completed Consensus Assessment Initiative Questionnaire (CAIQ) here.
Dialpad’s infrastructure and processes are annually certified against ISO 27001:2022 (Information security management), ISO 27017:2015 (Information Security in the cloud), and ISO 27018:2019 (PII for public cloud processors).

Securely enable your hybrid workforce
Sign a Data Processing Agreement (DPA) with one click to ensure that your business is set up to address data privacy requirements across Europe, the US, or wherever work finds you. Plus, every call with Dialpad uses WebRTC technology and Secure Real-Time Transport Protocol for encryption and authentication—making us more secure than traditional phone networks.

Record and transcribe calls with built-in privacy features
Record and transcribe calls with built-in privacy features Dialpad allows admins to configure call recording settings to comply with applicable laws—including the ability to play automated prompts to alert callers. Plus, in-call indicators make it clear whenever you’re recording. Granular controls can also pause recordings automatically whenever sensitive data is detected on screen.

Customize data retention and management
Dialpad offers analytics and export capabilities for sensitive data that can be managed by your admins. After all, your data belongs to you. We’ll retain data until you choose to delete it. Enterprise customers can set their own retention policies to remove, archive, or anonymize data on a custom time interval. Data subject requests are available in our help center.

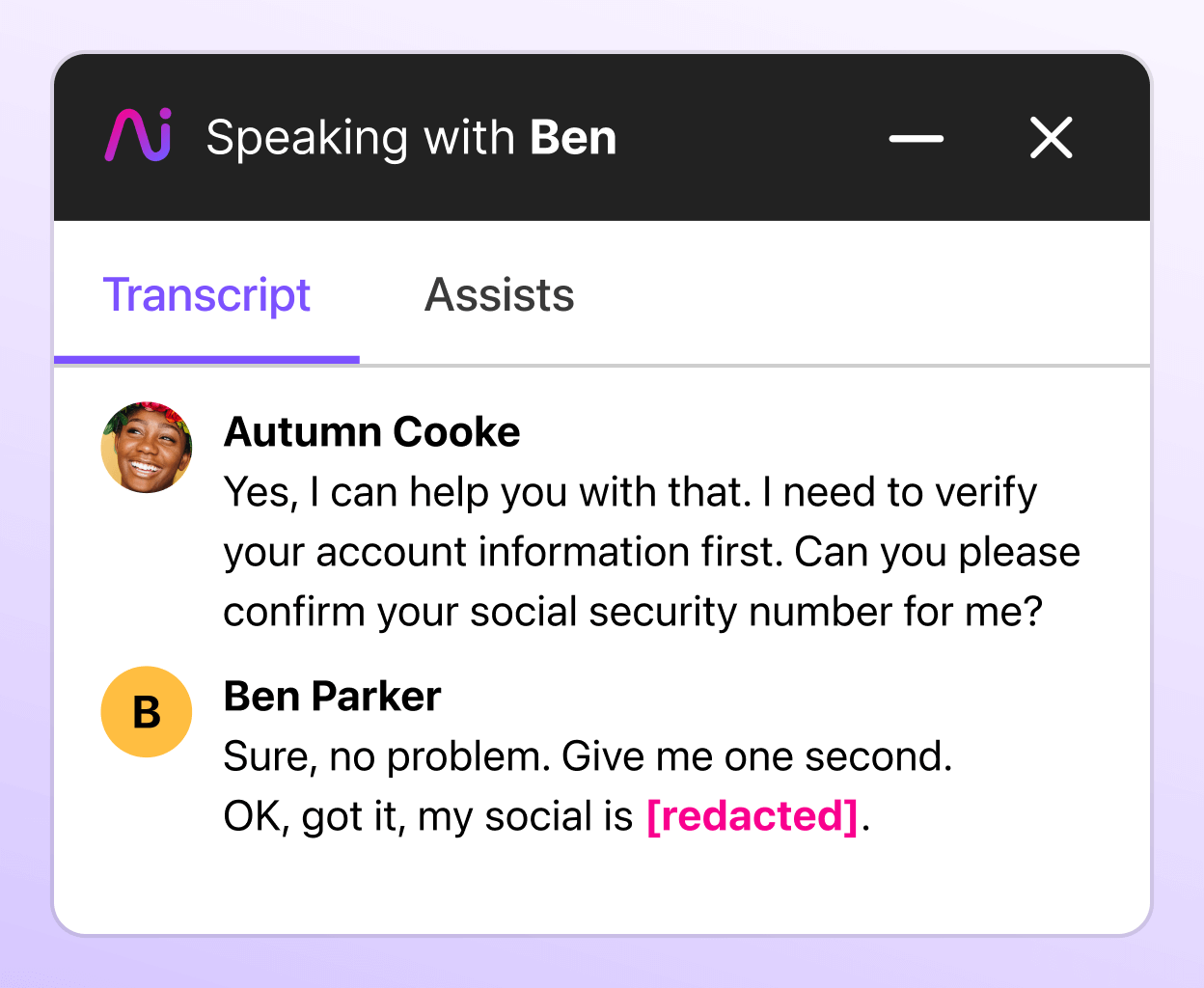
Protect sensitive information with Dialpad Ai’s PII Redaction
Dialpad PII Redaction is an Ai-driven feature designed to automatically identify and protect sensitive information in call transcripts. By leveraging machine learning algorithms to recognize and redact personal data, this capability ensures that personal identifiable data (PII) like credit card or social security numbers remain hidden from unauthorized eyes—while leaving the rest of the content intact.
More ways Dialpad helps you stay compliant
BLOG
Is Dialpad HIPAA-compliant?
EBOOK
A legal compliance guide for non-lawyers
BLOG
5 compliance features your contact center needs
Try Dialpad free for 14 days
Bring your business onto Dialpad’s enterprise-grade platform so your teams can talk, message, and meet all in one place.
